Supported Devices¶
Mirage allows to use multiple devices in order to interact with the supported wireless communications protocols.
Each device is identified by a short string called interface
Some capabilities are associated to each device, indicating what actions are available
The following page describes the available devices and their capabilities.
Bluetooth Low Energy Devices¶
HCI Device¶
Class : mirage.libs.ble.BLEHCIDevice

This device allows to communicate with an HCI Device in order to use Bluetooth Low Energy protocol.
The corresponding interfaces are : hciX (e.g. “hciX”)
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
yes |
ADVERTISING |
yes |
SNIFFING_ADVERTISEMENTS |
no |
SNIFFING_NEW_CONNECTION |
no |
SNIFFING_EXISTING_CONNECTION |
no |
JAMMING_CONNECTIONS |
no |
JAMMING_ADVERTISEMENTS |
no |
HIJACKING_MASTER |
no |
HIJACKING_SLAVE |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
INITIATING_CONNECTION |
yes |
RECEIVING_CONNECTION |
yes |
COMMUNICATING_AS_MASTER |
yes |
COMMUNICATING_AS_SLAVE |
yes |
HCI_MONITORING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
getConnections |
|
switchConnection |
|
getCurrentConnection |
|
getCurrentConnectionMode |
|
getAddressByHandle |
|
getCurrentHandle |
|
isConnected |
|
setScan |
|
setAdvertising |
|
setAdvertisingParameters |
|
setScanningParameters |
|
getAddress |
|
setAddress |
|
getMode |
|
getAddressMode |
|
getManufacturer |
|
isAddressChangeable |
|
encryptLink |
The detailed API is available here .
Note
BLEHCIDevice inherits from BtHCIDevice, that’s why some shared methods are provided by the BtHCIDevice API.
BTLEJack Device¶
Class : mirage.libs.ble_utils.btlejack.BTLEJackDevice

This device allows to communicate with a BTLEJack Device in order to sniff Bluetooth Low Energy protocol.
The corresponding interfaces are : microbitX (e.g. “microbit0”)
If you want to use a custom serial port in order to communicate with a Waveshare BLE400 or an NRF51 Development Kit embedding the BTLEJack firmware, you can use the following syntax while providing the interface to use: microbit:/dev/ttyXXXX (e.g. microbit:/dev/ttyACM0)
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
yes |
ADVERTISING |
no |
SNIFFING_ADVERTISEMENTS |
yes |
SNIFFING_NEW_CONNECTION |
yes |
SNIFFING_EXISTING_CONNECTION |
yes |
JAMMING_CONNECTIONS |
yes |
JAMMING_ADVERTISEMENTS |
yes |
HIJACKING_MASTER |
yes |
HIJACKING_SLAVE |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
INITIATING_CONNECTION |
no |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
yes |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
The detailed API is available here .
Ubertooth Device¶
Class : mirage.libs.ble_utils.ubertooth.BLEUbertoothDevice

This device allows to communicate with an Ubertooth Device in order to sniff Bluetooth Low Energy protocol.
The corresponding interfaces are : ubertoothX (e.g. “ubertooth0”)
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
yes |
ADVERTISING |
no |
SNIFFING_ADVERTISEMENTS |
yes |
SNIFFING_NEW_CONNECTION |
yes |
SNIFFING_EXISTING_CONNECTION |
yes |
JAMMING_CONNECTIONS |
yes |
JAMMING_ADVERTISEMENTS |
no |
HIJACKING_MASTER |
no |
HIJACKING_SLAVE |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
INITIATING_CONNECTION |
no |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
no |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
The detailed API is available here .
NRFSniffer Device¶
Class : mirage.libs.ble_utils.nrfsniffer.NRFSnifferDevice
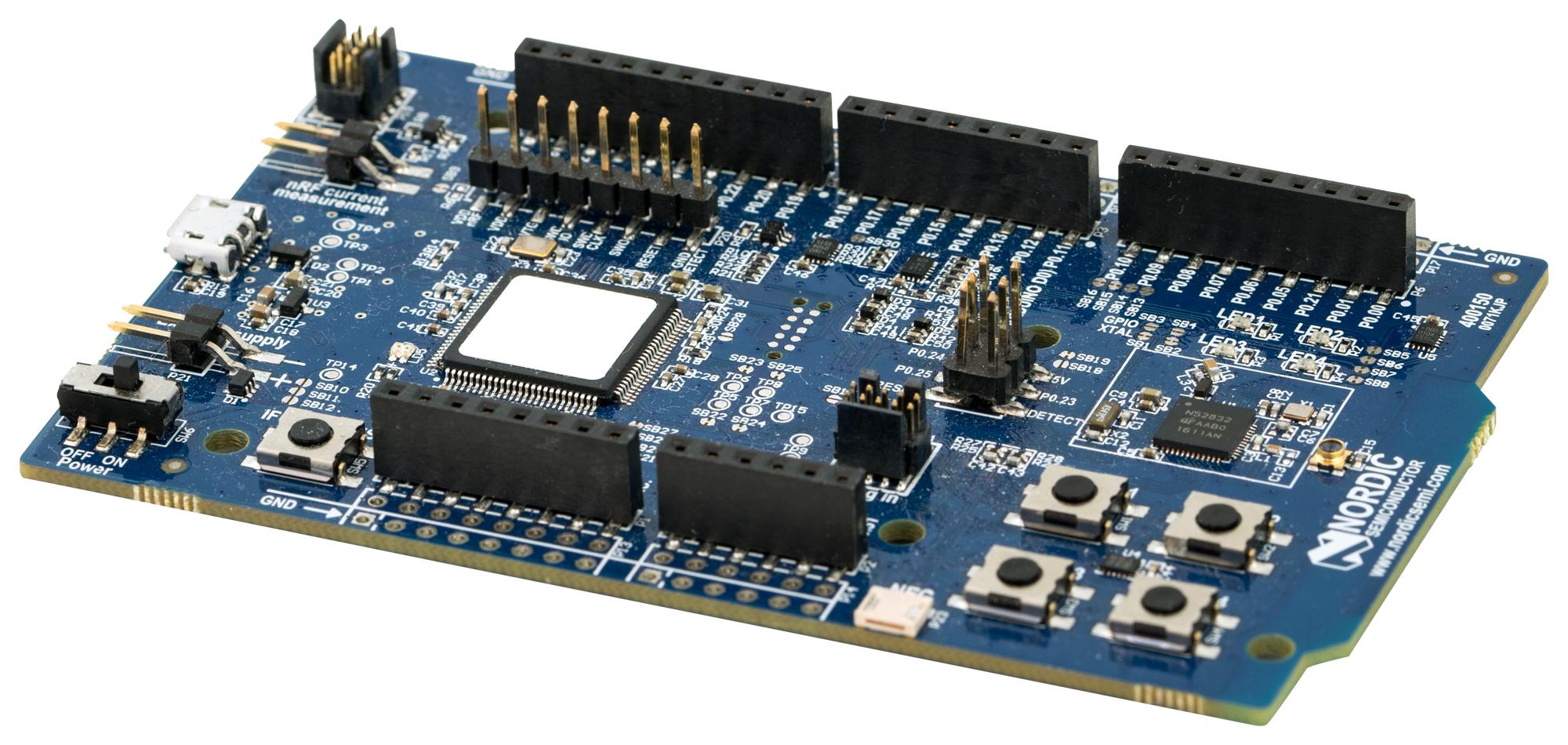
This device allows to communicate with a NRFSniffer Device in order to sniff Bluetooth Low Energy protocol.
The corresponding interfaces are : nrfsnifferX (e.g. “nrfsniffer0”)
If you want to use a custom serial port in order to communicate with a Waveshare BLE400 or an NRF51 Development Kit embedding the NRFSniffer firmware, you can use the following syntax while providing the interface to use: nrfsniffer:/dev/ttyXXXX (e.g. nrfsniffer:/dev/ttyACM0)
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
yes |
ADVERTISING |
no |
SNIFFING_ADVERTISEMENTS |
yes |
SNIFFING_NEW_CONNECTION |
yes |
SNIFFING_EXISTING_CONNECTION |
no |
JAMMING_CONNECTIONS |
no |
JAMMING_ADVERTISEMENTS |
no |
HIJACKING_MASTER |
no |
HIJACKING_SLAVE |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
INITIATING_CONNECTION |
no |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
no |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
The detailed API is available here .
Sniffle Device¶
Class : mirage.libs.ble_utils.sniffle.SniffleDevice
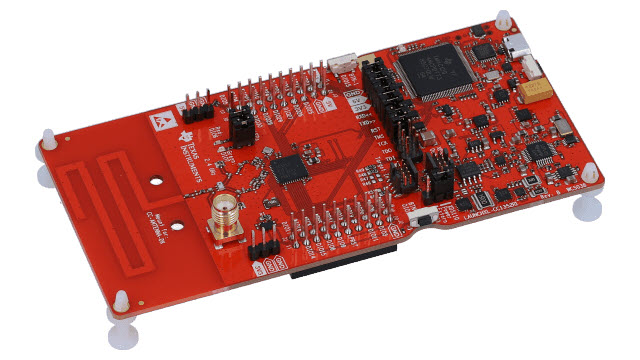
This device allows to communicate with a Sniffle Device in order to interact with Bluetooth Low Energy protocol.
The corresponding interfaces are : sniffleX (e.g. “sniffle0”)
If you want to use a custom serial port, you can use the following syntax while providing the interface to use: sniffle:/dev/ttyXXXX (e.g. sniffle:/dev/ttyACM0)
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
yes |
ADVERTISING |
yes |
SNIFFING_ADVERTISEMENTS |
yes |
SNIFFING_NEW_CONNECTION |
yes |
SNIFFING_EXISTING_CONNECTION |
no |
JAMMING_CONNECTIONS |
no |
JAMMING_ADVERTISEMENTS |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
HIJACKING_MASTER |
no |
HIJACKING_SLAVE |
no |
INITIATING_CONNECTION |
yes |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
yes |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
ButteRFly Device¶
Class : mirage.libs.ble_utils.butterfly.BLEButterflyDevice

This device allows to communicate with a ButteRFly Device in order to interact with Bluetooth Low Energy protocol.
A ButteRFly Device is a nRF52840 dongle embedding ButteRFly firmware, you can find instructions to flash the corresponding firmware here .
This device is needed to perform InjectaBLE attacks, such as packet injection into an established connection, slave or master hijacking, Man-in-the-Middle.
The corresponding interfaces are : butterflyX (e.g. “butterfly0”)
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
yes |
ADVERTISING |
no |
SNIFFING_ADVERTISEMENTS |
yes |
SNIFFING_NEW_CONNECTION |
yes |
SNIFFING_EXISTING_CONNECTION |
no |
JAMMING_CONNECTIONS |
no |
JAMMING_ADVERTISEMENTS |
no |
INJECTING |
yes |
MITMING_EXISTING_CONNECTION |
yes |
HIJACKING_MASTER |
yes |
HIJACKING_SLAVE |
yes |
INITIATING_CONNECTION |
no |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
no |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
HackRF Device¶
Class : mirage.libs.ble_utils.hackrf.BLEHackRFDevice

This device allows to communicate with a HackRF Device in order to interact with Bluetooth Low Energy protocol. HackRF support is experimental, the demodulator is slow and it can only deal with advertisements.
The corresponding interfaces are : hackrfX (e.g. “hackrf0”)
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
yes |
ADVERTISING |
yes |
SNIFFING_ADVERTISEMENTS |
yes |
SNIFFING_NEW_CONNECTION |
no |
SNIFFING_EXISTING_CONNECTION |
no |
JAMMING_CONNECTIONS |
no |
JAMMING_ADVERTISEMENTS |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
HIJACKING_MASTER |
no |
HIJACKING_SLAVE |
no |
INITIATING_CONNECTION |
no |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
no |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setChannel |
|
getChannel |
|
isConnected |
|
setAddress |
|
getAddress |
|
sniffAdvertisements |
mirage.libs.ble_utils.hackrf.BLEHackRFDevice.sniffAdvertisements |
setAdvertising |
|
setScanningParameters |
mirage.libs.ble_utils.hackrf.BLEHackRFDevice.setScanningParameters |
setAdvertisingParameters |
mirage.libs.ble_utils.hackrf.BLEHackRFDevice.setAdvertisingParameters |
setScan |
|
setScanInterval |
mirage.libs.ble_utils.hackrf.BLEHackRFDevice.setScanInterval |
getMode |
|
getFirmwareVersion |
mirage.libs.ble_utils.hackrf.BLEHackRFDevice.getFirmwareVersion |
getDeviceIndex |
|
getSerial |
|
getAPIVersion |
|
getBoardName |
|
getBoardID |
ADB Device¶
Class : mirage.libs.ble_utils.adb.ADBDevice
This device allows to communicate with an Android Device using adb in order to monitor Bluetooth Low Energy HCI packets.
The corresponding interfaces are : adbX (e.g. “adb0”)
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
no |
ADVERTISING |
no |
SNIFFING_ADVERTISEMENTS |
no |
SNIFFING_NEW_CONNECTION |
no |
SNIFFING_EXISTING_CONNECTION |
no |
JAMMING_CONNECTIONS |
no |
JAMMING_ADVERTISEMENTS |
no |
HIJACKING_MASTER |
no |
HIJACKING_SLAVE |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
INITIATING_CONNECTION |
no |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
no |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
yes |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Warning
You must install a recent version of adb in order to monitor a smartphone.
The full path to the binary adb should be present in the PATH environment variable.
You should enable the Developper mode, USB Debugging and Bluetooth logging on your smartphone.
If you don’t know how to configure your smartphone, please follow the instructions presented here.
The detailed API is available here .
HCIDump¶
Class : mirage.libs.ble_utils.hcidump.BLEHcidumpDevice
This device allows to monitor an HCI interface using hcidump.
The corresponding interfaces are : hcidumpX (e.g. “hcidump0” for monitoring the interface “hci0”).
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
no |
ADVERTISING |
no |
SNIFFING_ADVERTISEMENTS |
no |
SNIFFING_NEW_CONNECTION |
no |
SNIFFING_EXISTING_CONNECTION |
no |
JAMMING_CONNECTIONS |
no |
JAMMING_ADVERTISEMENTS |
no |
HIJACKING_MASTER |
no |
HIJACKING_SLAVE |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
INITIATING_CONNECTION |
no |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
no |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
yes |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
getConnections |
mirage.libs.ble_utils.hcidump.BLEHcidumpDevice.getConnections |
switchConnection |
mirage.libs.ble_utils.hcidump.BLEHcidumpDevice.switchConnection |
getCurrentConnection |
mirage.libs.ble_utils.hcidump.BLEHcidumpDevice.getCurrentConnection |
getAddressByHandle |
mirage.libs.ble_utils.hcidump.BLEHcidumpDevice.getAddressByHandle |
getCurrentHandle |
mirage.libs.ble_utils.hcidump.BLEHcidumpDevice.getCurrentHandle |
getCurrentConnectionMode |
mirage.libs.ble_utils.hcidump.BLEHcidumpDevice.getCurrentConnectionMode |
isConnected |
|
getHCIInterface |
mirage.libs.ble_utils.hcidump.BLEHcidumpDevice.getHCIInterface |
getDeviceIndex |
mirage.libs.ble_utils.hcidump.BLEHcidumpDevice.getDeviceIndex |
Warning
You must install a recent version of hcidump in order to monitor an HCI device.
The full path to the binary hcidump should be present in the PATH environment variable.
The detailed API is available here .
BLE PCAP Files¶
Class : mirage.libs.ble_utils.pcap.BLEPCAPDevice
This device allows to communicate with a PCAP file in order to write and read Bluetooth Low Energy packets.
The corresponding interfaces are : <filename>.pcap (e.g. “out.pcap”)
If the file exists, the BLEPCAPDevice is in read mode, and the corresponding receiver is able to use it as a classic Bluetooth Low Energy sniffer.
If the file doesn’t exist, the BLEPCAPDevice is in write mode, and the corresponding emitter is able to write packets in the file.
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SCANNING |
no |
ADVERTISING |
no |
SNIFFING_ADVERTISEMENTS |
yes |
SNIFFING_NEW_CONNECTION |
yes |
SNIFFING_EXISTING_CONNECTION |
no |
JAMMING_CONNECTIONS |
no |
JAMMING_ADVERTISEMENTS |
no |
HIJACKING_MASTER |
no |
HIJACKING_SLAVE |
no |
INJECTING |
no |
MITMING_EXISTING_CONNECTION |
no |
INITIATING_CONNECTION |
no |
RECEIVING_CONNECTION |
no |
COMMUNICATING_AS_MASTER |
no |
COMMUNICATING_AS_SLAVE |
no |
HCI_MONITORING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
sniffNewConnections |
mirage.libs.ble_utils.pcap.BLEPCAPDevice.sniffNewConnections |
sniffAdvertisements |
mirage.libs.ble_utils.pcap.BLEPCAPDevice.sniffAdvertisements |
getAccessAddress |
|
getCrcInit |
|
getChannelMap |
|
getHopInterval |
|
getHopIncrement |
|
isSynchronized |
|
getMode |
Warning
This PCAP Device uses the DLT 256, and can be used to read or write some Link Layer packets. It is not compatible with a PCAP file containing HCI frames.
The detailed API is available here .
Enhanced ShockBurst Devices¶
ESB RFStorm Device¶
Class : mirage.libs.esb_utils.rfstorm.ESBRFStormDevice

This device allows to interact with a NRF24-based device embedding the RFStorm firmware (also called nrf-research-firmware). This firmware can be installed on a Crazy Radio PA or some Logitech Unifying dongle, please refer to the documentation provided by Bastille Research for more details.
The corresponding interfaces are : rfstormX (e.g. “rfstorm0”).
The following capabilities are currently supported :
Capability |
Available ? |
|---|---|
INJECTING |
yes |
SNIFFING_NORMAL |
yes |
SNIFFING_PROMISCUOUS |
yes |
SNIFFING_GENERIC_PROMISCUOUS |
yes |
ACTIVE_SCANNING |
yes |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setChannel |
|
getChannel |
|
getDeviceIndex |
mirage.libs.esb_utils.rfstorm.ESBRFStormDevice.getDeviceIndex |
enterPromiscuousMode |
mirage.libs.esb_utils.rfstorm.ESBRFStormDevice.enterPromiscuousMode |
enterGenericPromiscuousMode |
mirage.libs.esb_utils.rfstorm.ESBRFStormDevice.enterGenericPromiscuousMode |
enterSnifferMode |
mirage.libs.esb_utils.rfstorm.ESBRFStormDevice.enterSnifferMode |
getMode |
|
getAddress |
|
setAddress |
|
isAutoAckEnabled |
mirage.libs.esb_utils.rfstorm.ESBRFStormDevice.isAutoAckEnabled |
enableAutoAck |
mirage.libs.esb_utils.rfstorm.ESBRFStormDevice.enableAutoAck |
disableAutoAck |
mirage.libs.esb_utils.rfstorm.ESBRFStormDevice.disableAutoAck |
scan |
The detailed API is available here .
ESB PCAP Files¶
Class : mirage.libs.ble_utils.pcap.ESBPCAPDevice
This device allows to communicate with a PCAP file in order to write and read Enhanced ShockBurst packets.
The corresponding interfaces are : <filename>.pcap (e.g. “out.pcap”)
If the file exists, the ESBPCAPDevice is in read mode, and the corresponding receiver is able to use it as a classic Enhanced ShockBurst sniffer.
If the file doesn’t exist, the ESBPCAPDevice is in write mode, and the corresponding emitter is able to write packets in the file.
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
INJECTING |
yes |
SNIFFING_NORMAL |
yes |
SNIFFING_PROMISCUOUS |
yes |
SNIFFING_GENERIC_PROMISCUOUS |
no |
ACTIVE_SCANNING |
yes |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setChannel |
|
getChannel |
|
enterPromiscuousMode |
mirage.libs.esb_utils.pcap.ESBPCAPDevice.enterPromiscuousMode |
enterSnifferMode |
|
getMode |
|
generateStream |
|
scan |
Warning
This PCAP Device uses the DLT 148.
The detailed API is available here .
Mosart Devices¶
Mosart RFStorm Device¶
Class : mirage.libs.mosart_utils.rfstorm.MosartRFStormDevice

This device allows to interact with a NRF24-based device embedding the RFStorm firmware (also called nrf-research-firmware). This firmware can be installed on a Crazy Radio PA or some Logitech Unifying dongle, please refer to the documentation provided by Bastille Research for more details.
The corresponding interfaces are : rfstormX (e.g. “rfstorm0”).
The following capabilities are currently supported :
Capability |
Available ? |
|---|---|
SNIFFING_NORMAL |
yes |
SNIFFING_PROMISCUOUS |
yes |
INJECTING |
yes |
INJECTING_SYNC |
yes |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
The detailed API is available here .
Mosart PCAP Files¶
Class : mirage.libs.mosart_utils.pcap.MosartPCAPDevice
This device allows to communicate with a PCAP file in order to write and read Mosart packets.
The corresponding interfaces are : <filename>.pcap (e.g. “out.pcap”)
If the file exists, the MosartPCAPDevice is in read mode, and the corresponding receiver is able to use it as a classic Mosart sniffer.
If the file doesn’t exist, the MosartPCAPDevice is in write mode, and the corresponding emitter is able to write packets in the file.
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SNIFFING_NORMAL |
yes |
SNIFFING_PROMISCUOUS |
yes |
INJECTING |
yes |
INJECTING_SYNC |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setChannel |
|
getChannel |
|
enterPromiscuousMode |
mirage.libs.mosart_utils.pcap.MosartPCAPDevice.enterPromiscuousMode |
enterSnifferMode |
mirage.libs.mosart_utils.pcap.MosartPCAPDevice.enterSnifferMode |
getMode |
|
generateStream |
mirage.libs.mosart_utils.pcap.MosartPCAPDevice.generateStream |
enableDonglePackets |
mirage.libs.mosart_utils.pcap.MosartPCAPDevice.enableDonglePackets |
disableDonglePackets |
mirage.libs.mosart_utils.pcap.MosartPCAPDevice.disableDonglePackets |
Warning
This PCAP Device uses the DLT 149.
The detailed API is available here .
WiFi Devices¶
WiFi Device¶
Class : mirage.libs.wifi.WifiDevice

This device allows to communicate with a WiFi Device.
The corresponding interfaces are : wlanX (e.g. “wlanX”)
The following capabilities are currently supported :
Capability |
Available ? |
|---|---|
SCANNING |
yes |
MONITORING |
yes |
COMMUNICATING_AS_ACCESS_POINT |
yes |
COMMUNICATING_AS_STATION |
yes |
JAMMING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setChannel |
|
getChannel |
|
setFrequency |
|
getFrequency |
|
setMonitorMode |
|
getAddress |
|
setMode |
|
getMode |
The detailed API is available here .
Zigbee Devices¶
RZUSBStick Device¶
Class : mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice

This device allows to communicate with a Raven RZUSBStick Device.
The corresponding interfaces are : rzusbstickX (e.g. “rzusbstickX”)
The following capabilities are currently supported :
Capability |
Available ? |
|---|---|
SNIFFING |
yes |
INJECTING |
yes |
COMMUNICATING_AS_COORDINATOR |
yes |
COMMUNICATING_AS_ROUTER |
yes |
COMMUNICATING_AS_END_DEVICE |
yes |
JAMMING |
yes |
Warning
Some features provided by this hardware seems unstable :
A small amount of time is required to switch from TX to RX, so some frames may be missing
The jamming feature seems to send a very short signal which is not strong and long enough to jam a Zigbee channel
I’m not sure if the problem is linked to my hardware or if the Killerbee firmare is buggy.
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setChannel |
mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice.setChannel |
getChannel |
mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice.getChannel |
enableJamming |
mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice.enableJamming |
disableJamming |
mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice.disableJamming |
getMode |
mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice.getMode |
getFirmwareVersion |
mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice.getFirmwareVersion |
getSerial |
mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice.getSerial |
getDeviceIndex |
mirage.libs.zigbee_utils.rzusbstick.RZUSBStickDevice.getDeviceIndex |
The detailed API is available here .
HackRF Device¶
Class : mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice

This device allows to communicate with a HackRF in order to interact with the Zigbee protocol. HackRF support is experimental, the demodulator is slow !
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SNIFFING |
yes |
INJECTING |
yes |
COMMUNICATING_AS_COORDINATOR |
no |
COMMUNICATING_AS_ROUTER |
no |
COMMUNICATING_AS_END_DEVICE |
no |
JAMMING |
no |
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setChannel |
mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice.setChannel |
getChannel |
mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice.getChannel |
getFirmwareVersion |
mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice.getFirmwareVersion |
getDeviceIndex |
mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice.getDeviceIndex |
getSerial |
mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice.getSerial |
getAPIVersion |
mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice.getAPIVersion |
getBoardName |
mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice.getBoardName |
getBoardID |
mirage.libs.zigbee_utils.hackrf.ZigbeeHackRFDevice.getBoardID |
Zigbee PCAP Files¶
Class : mirage.libs.zigbee_utils.pcap.ZigbeePCAPDevice
This device allows to communicate with a PCAP file in order to write and read Zigbee packets.
The corresponding interfaces are : <filename>.pcap (e.g. “out.pcap”)
If the file exists, the ZigbeePCAPDevice is in read mode, and the corresponding receiver is able to use it as a classic Zigbee sniffer.
If the file doesn’t exist, the ZigbeePCAPDevice is in write mode, and the corresponding emitter is able to write packets in the file.
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SNIFFING |
yes |
INJECTING |
yes |
COMMUNICATING_AS_COORDINATOR |
no |
COMMUNICATING_AS_ROUTER |
no |
COMMUNICATING_AS_END_DEVICE |
no |
JAMMING |
no |
Warning
This PCAP Device uses the DLT 195.
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setChannel |
|
getChannel |
|
generateStream |
mirage.libs.zigbee_utils.pcap.ZigbeePCAPDevice.generateStream |
getMode |
The detailed API is available here .
Infrared Radiations Devices¶
IRMA Device¶
Class : mirage.libs.ir_utils.irma.IRMADevice
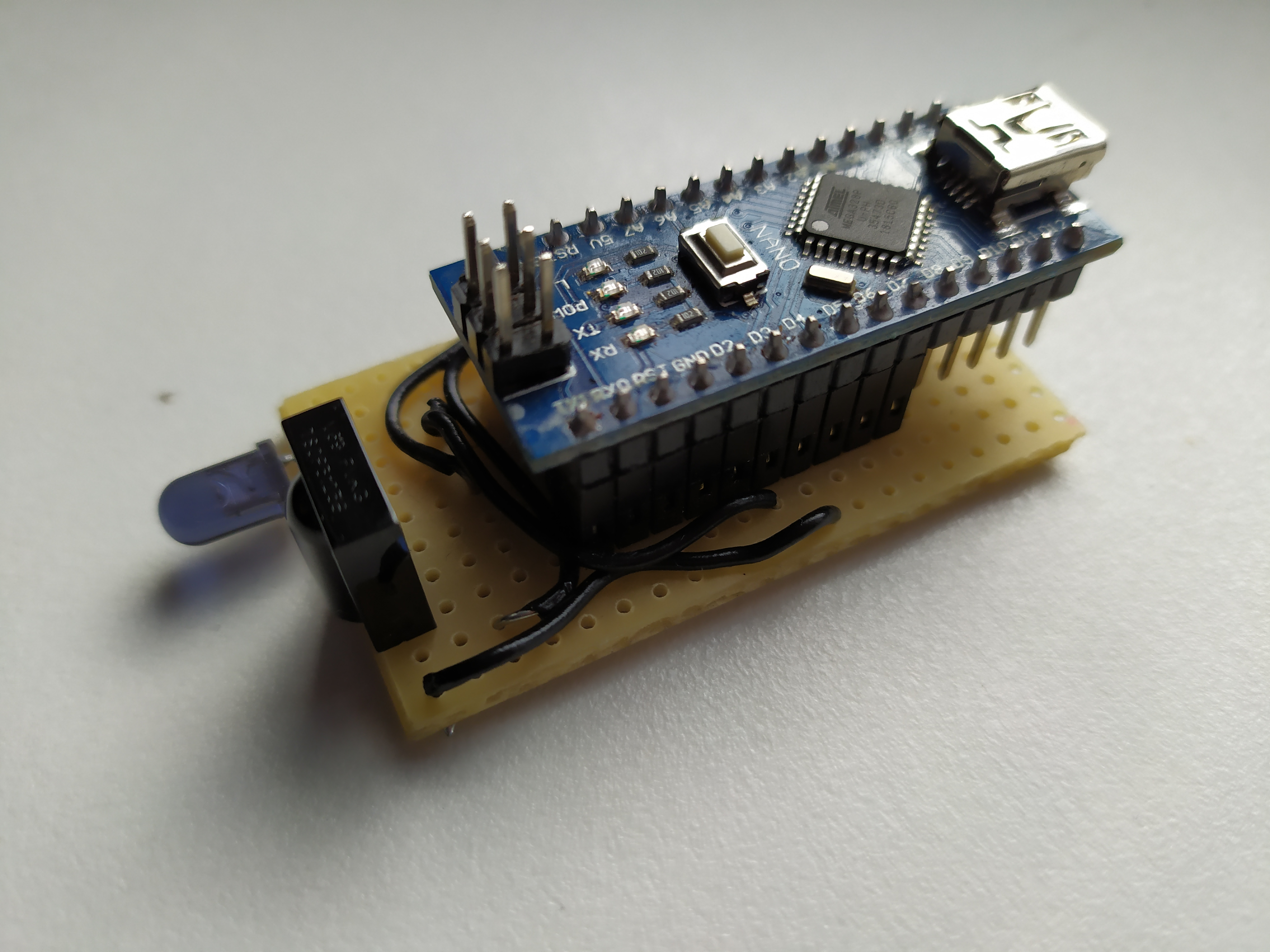
This device allows to communicate with an IRMA device in order to sniff and inject IR signals.
The corresponding interfaces are : irmaX (e.g. “irma0”).
The following capabilities are actually supported :
Capability |
Available ? |
|---|---|
SNIFFING |
yes |
INJECTING |
yes |
CHANGING_FREQUENCY |
yes |
Warning
This device has been created in order to interact with IR signals using Mirage. It requires an Arduino Uno or Mini, and the electronic schematic and firmware source code are released as open source documents. You can download the resources needed to build this device here.
The following methods are shared and can be used directly from the corresponding Emitter and/or Receiver :
Shared Methods |
Corresponding documentation |
|---|---|
setFrequency |
|
getFrequency |
|
waitData |
|
reset |
|
getSerialPort |
|
getDeviceIndex |
The detailed API is available here .